Incidents test more than infrastructure. They test coordination, accountability, and internal discipline. When multiple teams are working under pressure, unclear permissions can quickly create confusion. Someone may close an incident prematurely. Someone else may escalate severity without authority. Sensitive notes might become visible to the wrong audience. This is where Role-Based Access Control in incident management becomes critical.
In incident management, RBAC is not simply a security setting. It is a framework that defines who can take action, who can access sensitive data, and who is responsible for communication. When implemented correctly, it protects both systems and workflows.
What Role-Based Access Control Means in Incident Management
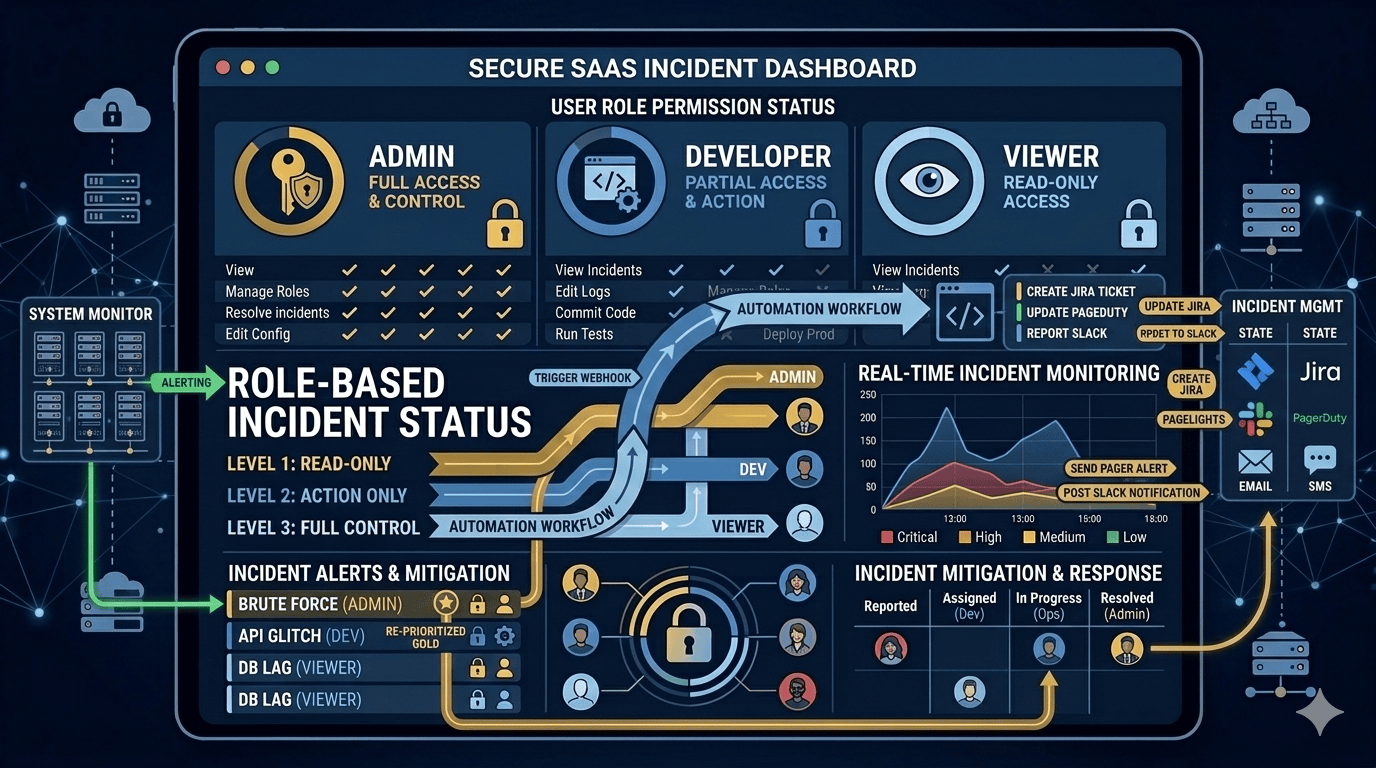
Role-Based Access Control assigns permissions to roles rather than individuals. Users inherit access based on the role they are assigned within the organization.
In an incident management environment, roles often include incident responders, on-call engineers, incident commanders, support agents, communication leads, and executive stakeholders. Each of these roles carries different responsibilities. An engineer may need access to logs and system details. A communications lead may need permission to publish external updates. An executive may require visibility without operational editing rights.
By defining permissions at the role level, organizations avoid overexposing sensitive functions while keeping workflows efficient.
Why Access Control Becomes Critical During Incidents
During high-severity incidents, speed is important, but so is control. When permissions are too broad, small mistakes can create larger problems. An unauthorized severity change can trigger unnecessary escalations. A premature resolution can mislead stakeholders. Unrestricted access to internal notes can expose sensitive information.
Incidents often involve details about vulnerabilities, infrastructure architecture, and customer impact. Without structured access control, the risk extends beyond operational disruption into compliance and reputational exposure.
RBAC ensures that every action taken during an incident is intentional and traceable.
A Practical Example: When Permissions Go Wrong
Consider a high-severity security incident affecting a customer-facing application. Multiple teams join the response bridge. Logs are being reviewed, patches are being tested, and customer impact is still unclear.
Without structured access control, a well-intentioned team member might downgrade the severity prematurely after a temporary mitigation appears successful. Another person may close the incident to reduce internal pressure, assuming the issue is resolved. Meanwhile, sensitive investigation notes remain visible to individuals who do not need access.
In contrast, with properly defined roles, only the incident commander has the authority to adjust severity levels. Only designated communications leads can publish external updates.
Investigative notes are restricted to responders directly involved in remediation. The workflow remains controlled, and accountability is preserved.
This difference may seem procedural, but during high-pressure incidents, it directly affects risk exposure and organizational trust.
Security Considerations in RBAC for Incident Management
One of the most important principles behind RBAC is least privilege. Each user should have only the access required to perform their role. This reduces the risk of accidental or malicious changes without slowing legitimate work.
Incident records can contain sensitive data, including security indicators, customer information, and internal remediation steps. Access to these elements should be restricted based on operational necessity. Limiting visibility protects both organizational integrity and regulatory compliance.
Equally important is auditability. In many industries, incident handling processes are reviewed for compliance. Clear role definitions ensure that every action is attributable and that permission boundaries are documented. This strengthens accountability and simplifies audit preparation.
Workflow Considerations for Team Permissions
Access control does more than protect data. It shapes how incident response unfolds.
When roles are clearly defined, responsibility becomes clearer. Only designated leaders should have the authority to escalate severity to critical levels. Only approved communication leads should publish external updates. This prevents conflicting messages and reduces decision bottlenecks.
At the same time, permissions must reflect real workflows. Overly restrictive controls can slow response if critical actions depend on a single individual. Effective RBAC balances restriction with operational flexibility. The goal is to create structure without introducing unnecessary delays.
Separation of duties is another important consideration. Investigation, approval of external communication, and execution of remediation steps should not always sit with the same individual. Dividing authority reduces bias and lowers the chance of compounding errors during high-pressure situations.
Designing RBAC for Incident Management Systems
Implementing RBAC effectively requires thoughtful planning.
The first step is mapping the incident workflow. Identify who detects incidents, who investigates them, who communicates externally, and who approves resolution. Access controls should mirror these real-world responsibilities.
Next, define permission categories carefully. Viewing incidents, editing details, changing severity, assigning responders, accessing logs, publishing public updates, and closing incidents should be separate permissions rather than bundled together. Granular control provides flexibility while maintaining security boundaries.
Finally, review access regularly. Teams evolve. New services are added. Employees change roles. Without periodic review, permissions become outdated and risky. RBAC must adapt alongside organizational change.
Common Mistakes in Role-Based Access Control
Organizations often undermine their own access controls by granting overly broad administrative rights for convenience. While this may simplify onboarding, it weakens long-term security posture.
Another frequent mistake is failing to revoke temporary elevated access granted during major incidents. Emergency permissions should not become permanent privileges.
RBAC also fails when roles are defined loosely or tied to specific individuals instead of functional responsibilities. Clear role definitions ensure continuity even as team members transition.
With and Without RBAC: A Direct Comparison
| Without Structured RBAC | With Structured RBAC |
| Broad permissions granted for convenience | Permissions aligned strictly with defined roles |
| Multiple users can modify severity or close incidents | Escalation and closure authority limited to designated roles |
| Sensitive investigation data visible to wide audiences | Sensitive data restricted to operationally relevant roles |
| Inconsistent communication updates | Controlled publishing rights ensure message consistency |
| Limited audit clarity during reviews | Clear accountability with traceable actions |
| Higher risk of workflow confusion | Structured decision flow under pressure |
The technical systems may be identical in both cases. What changes is governance. Structured permissions reduce risk without slowing operational response.
RBAC and Communication Integrity
Incident communication is particularly sensitive. Inconsistent updates can damage trust quickly. If multiple team members have unrestricted authority to edit public-facing updates, messaging can become fragmented or contradictory.
Restricting external communication permissions ensures that updates remain accurate, legally sound, and consistent in tone. Structured communication platforms such as Incipulse allow organizations to define who can publish updates and who has internal visibility only. This separation supports transparency while maintaining discipline.
The Business Impact of Strong Access Control
Role-Based Access Control in incident management strengthens more than security. It enhances operational maturity.
Clear permissions reduce accidental errors. They protect sensitive information, reinforce accountability, and improve audit readiness. They also maintain workflow clarity during complex incidents.
In enterprise environments, poorly managed permissions during an incident can amplify damage. Strong access control limits that exposure and reinforces trust internally and externally.
Conclusion
Role-Based Access Control brings structure to incident management. By defining clear permissions aligned with operational roles, organizations protect sensitive data and maintain workflow discipline under pressure.
Incidents will always introduce complexity. RBAC ensures that complexity does not turn into chaos. For teams operating at scale, it is not an optional feature but a foundational component of resilient incident response.
FAQs
How does RBAC improve incident response efficiency?
RBAC improves efficiency by clearly defining who can take which actions during an incident. When escalation authority, communication rights, and system access are aligned with roles, teams avoid confusion and reduce decision bottlenecks under pressure.
Can RBAC help with compliance requirements?
Yes. In regulated industries, incident records must demonstrate accountability and controlled access. RBAC ensures that actions are traceable, permissions are structured, and sensitive data is accessible only to authorized roles. This strengthens audit readiness and regulatory compliance.
What is the difference between RBAC and basic user permissions?
Basic user permissions are often assigned individually and inconsistently. RBAC groups permissions into structured roles tied to responsibilities. This makes access easier to manage, scale, and review as teams grow or change.
How often should RBAC policies be reviewed in incident management systems?
RBAC policies should be reviewed periodically, especially after organizational restructuring, team expansion, service additions, or major incidents. Regular review ensures that permissions reflect actual responsibilities rather than outdated assumptions.
Can overly strict RBAC slow incident response?
Yes, if designed poorly. Effective RBAC balances security with operational flexibility. Critical responders must have sufficient authority to act quickly without unnecessary approval bottlenecks.